root@linxploit:~$ █
HAMID
AI-Based Blockchain & Offensive Security Learner
[ Founder @ Linxploit ]
Exploring Offensive Security, AI Systems, and Digital Psychology
"If you ever miss me, just remember I am as far away as you pushed me!"
root@linxploit:~$ █
[ Founder @ Linxploit ]
Exploring Offensive Security, AI Systems, and Digital Psychology
$ cat /etc/profile/hamid
NAME: Hamid
ROLE: Offensive Security Student & Startup Founder
FOCUS: Offensive Security | AI Security | Blockchain
$ ./describe --full
A relentless explorer at the intersection of artificial intelligence, blockchain security, and offensive cyber operations. I approach security not as a profession — but as a goal.
From reverse engineering hardware with Flipper Zero to weaponizing AI for red-team operations, my work pushes the boundaries of what ethical hacking can achieve in a digitally weaponized world.
Beyond the technical, I study dark psychology, human behavioral manipulation, and the strategic warfare of the mind — because the greatest vulnerability in any system is always human.
$ cat interests.txt
Network defense, threat modeling, vulnerability assessment and security architecture design.
Exploitation frameworks, payload crafting, privilege escalation, and post-exploitation.
Full-scope pentest methodology, web app testing, infrastructure assessments and red-team ops.
Open-source intelligence gathering, footprinting, digital forensics, and target profiling.
Adversarial ML, AI red-teaming, prompt injection, model extraction and AI threat vectors.
Smart contract auditing, DeFi exploit analysis, consensus attacks, and Web3 vulnerabilities.
TCP/IP, packet analysis, MITM attacks, protocol exploitation, and network forensics.
Kali, BlackArch, system hardening, kernel exploits, privilege escalation, and scripting.
Dark psychology, social engineering, behavioral profiling, manipulation detection, and influence ops.
Weaponized toolkit of an offensive security operator
World's most used penetration testing framework for exploit development and execution.
Browser Exploitation Framework for assessing web browser security and hooked client attacks.
Multi-tool device for hardware hacking, RF signals, RFID cloning, and physical security testing.
Portable network monitoring and packet sniffing tool for wireless attack operations.
Debian-based Linux distribution built for penetration testing and digital forensics.
Arch Linux-based distro with 2800+ security tools for advanced security researchers.
Industry-standard web vulnerability scanner and proxy for web application penetration testing.
Network mapper for discovery, port scanning, OS fingerprinting and service enumeration.
Deep packet inspection and protocol analysis for network traffic forensics.
OSINT and graphical link analysis tool for mapping relationships and digital footprints.
Rogue access point platform for intercepting wireless communications and man-in-the-middle attacks.
Comprehensive open-source intelligence toolkit for target profiling, data aggregation, and surveillance.
linxploit.xyz
Linxploit is a cybersecurity initiative built on the philosophy that understanding the attacker is the only true defense.
We operate at the bleeding edge of offensive security research, vulnerability discovery, and digital threat intelligence — delivering clarity in a world of evolving cyber threats.
Where Ancient Philosophy meets Modern Psychological Operations
"Know the enemy and know yourself; in a hundred battles, you will never be in peril."
"The obstacle is the way. The impediment to action advances action. What stands in the way becomes the way."
"He who controls others may be powerful, but he who has mastered himself is mightier still."
Classified research and operational tools
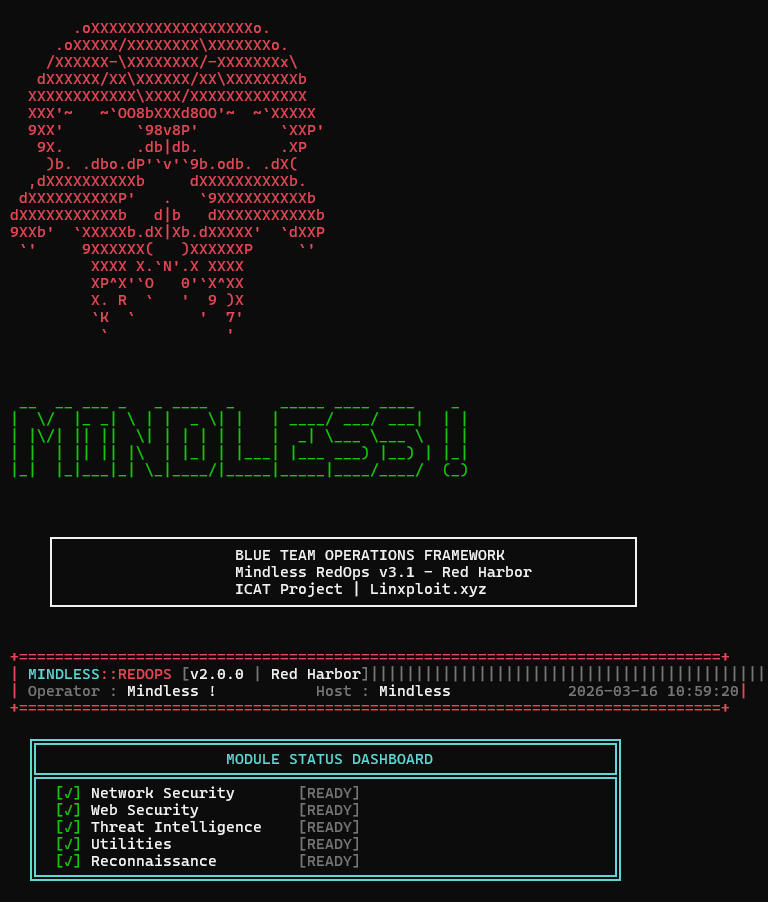
A modular offensive security toolkit designed to integrate multiple reconnaissance, scanning, and exploitation utilities into a unified testing environment.
View Details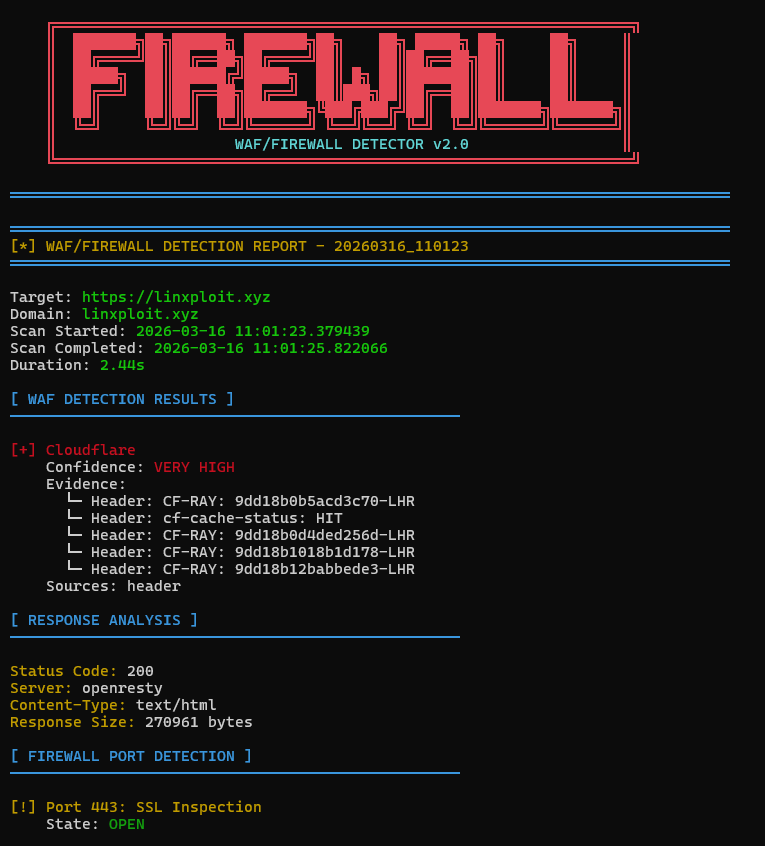
Identifies whether a target website is protected by a Web Application Firewall by analyzing HTTP responses, headers, and filtering behavior.
View Details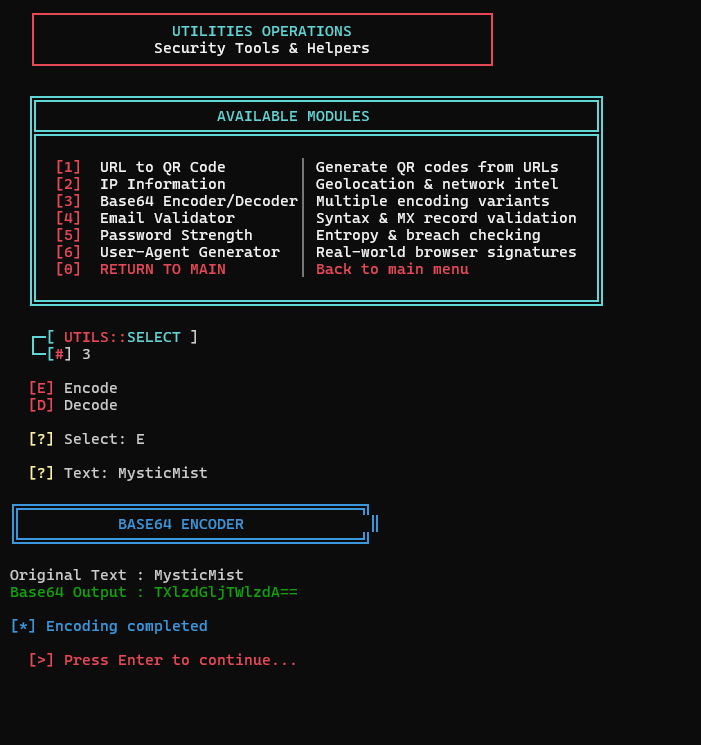
Encodes and decodes data using the Base64 scheme, commonly used in web technologies, authentication headers, and data transmission.
View Details
Discovers hidden directories and files on web servers by sending automated requests using wordlists to map potential attack surfaces.
View Details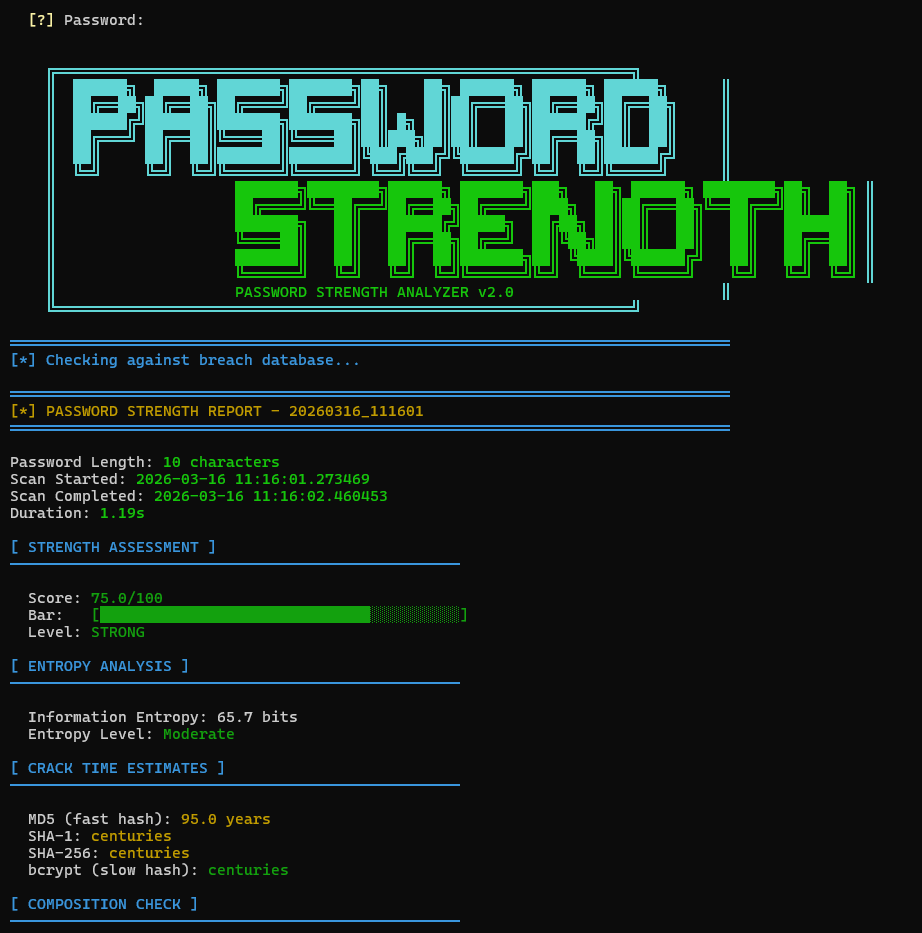
Analyzes password complexity and entropy to evaluate resistance against brute-force and dictionary attacks.
View Details
Analyzes password complexity and entropy to evaluate resistance against brute-force and dictionary attacks.
View Details
Scans target hosts to identify open ports and active services, helping analyze network exposure during security assessments.
View Details
Inspects SSL/TLS configurations of websites to detect weak ciphers, certificate issues, and potential encryption vulnerabilities.
View Details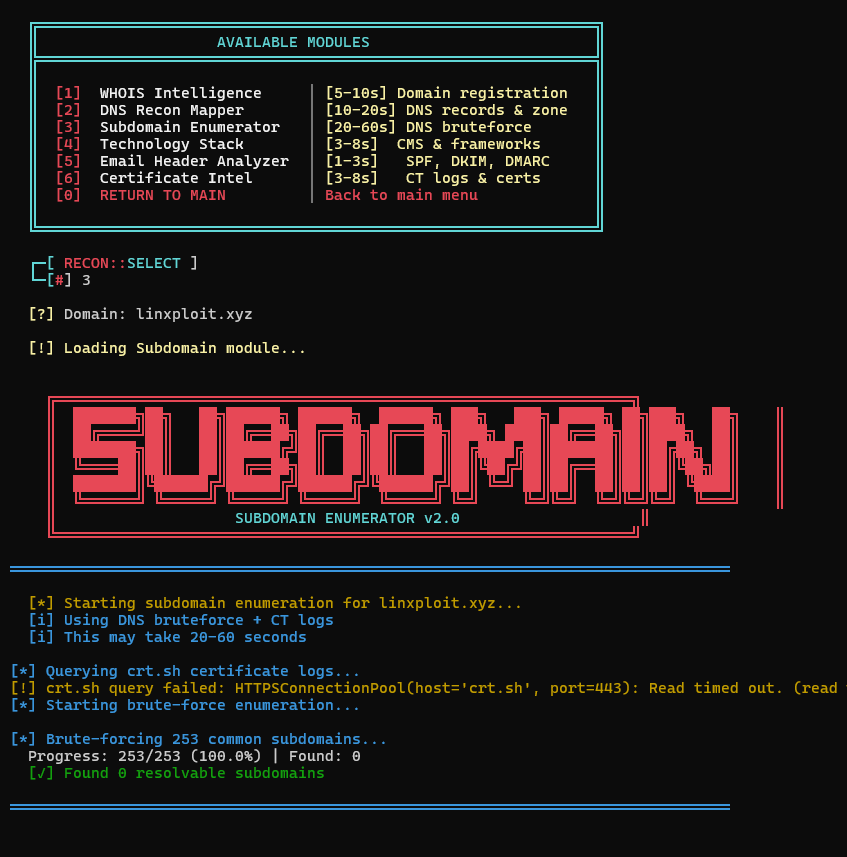
Enumerates subdomains associated with a target domain using automated discovery techniques to expand the attack surface map.
View Details
A wireless reconnaissance utility designed to monitor nearby Wi-Fi networks and collect technical information about access points and devices.
View DetailsNew Projects Coming
// CLASSIFIED //$ ./initiate_contact --mode secure
Establishing encrypted channel...
[OK] Secure connection established
Available contact vectors: